The Cybersecurity Email Paradox
You sell security, so your email practices need to be bulletproof. Your audience - CISOs, security engineers, and IT managers - will check your SPF records, notice if DKIM fails, and judge your company by your email authentication setup. Before choosing an email tool, ensure it supports full email authentication and your sender reputation is spotless.
The Long Sales Cycle Problem
Cybersecurity enterprise sales take 6-18 months. During that time, your leads are evaluating multiple vendors, reading analyst reports, and navigating internal procurement. Email is your primary tool for staying relevant during this evaluation. Monthly threat digests, quarterly compliance updates, and event-triggered nurture sequences keep you top of mind.
Thought Leadership Through Email
The most effective cybersecurity email marketing is not marketing at all - it is thought leadership. Threat intelligence, compliance guides, and incident response best practices position your company as an expert. When the buying decision comes, the vendor who has been providing the most valuable security content has a significant advantage.
Choosing the Right Email Tool for Cybersecurity
Cybersecurity companies need email tools that meet three requirements most marketing platforms were not designed for:
Authentication and data handling must be impeccable. Your audience checks your email authentication. Choose a platform with full SPF, DKIM, and DMARC support and verify everything before sending your first email. Additionally, review the email platform's own security practices - SOC 2 compliance, data encryption, and access controls matter when your brand is security.
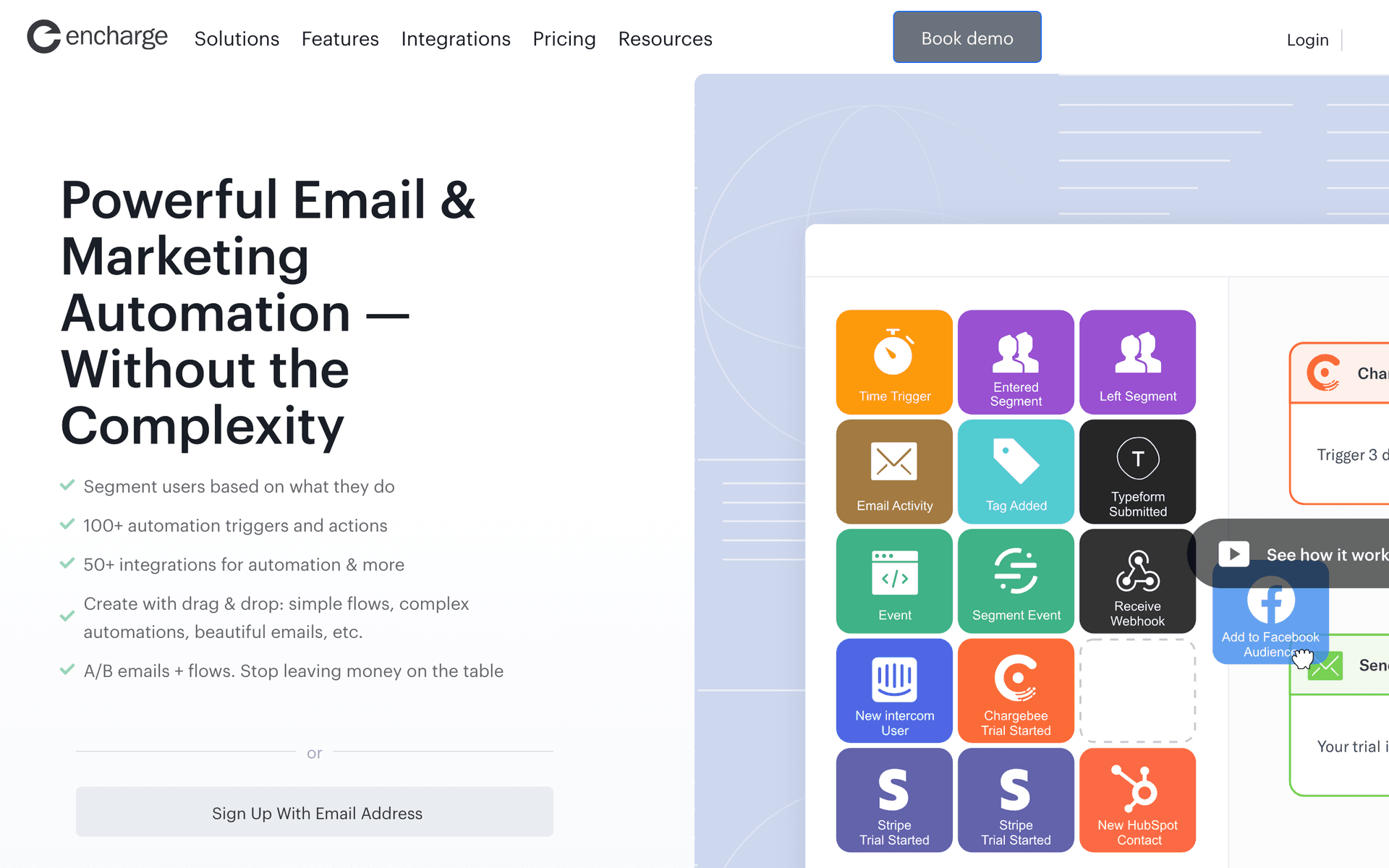
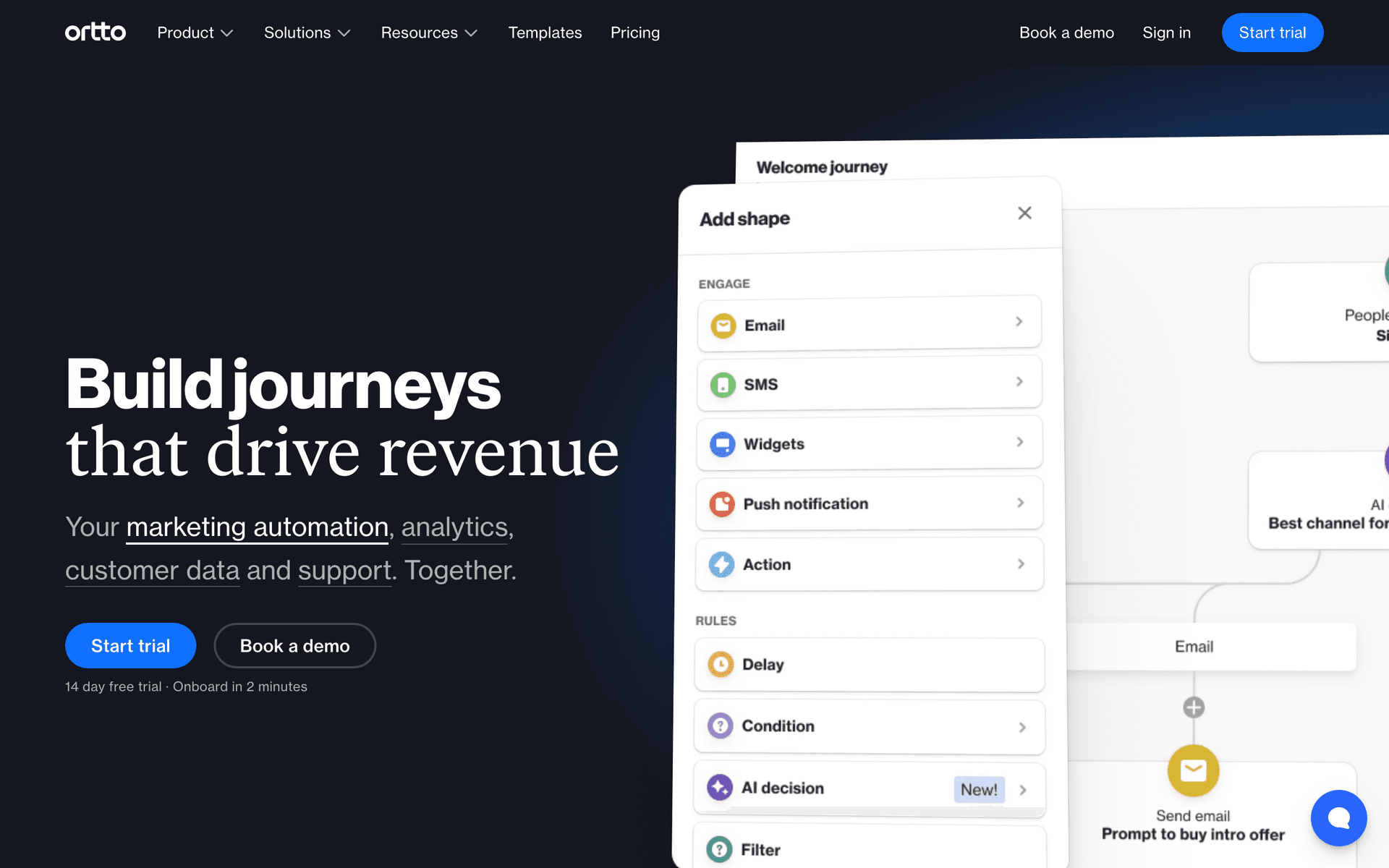
Event-driven automation for product communication. Cybersecurity products generate events - scans completed, threats detected, policies configured. Your email tool needs to trigger sequences based on these product events, not just time-based delays. Sequenzy and Customer.io handle this natively.
Separate infrastructure for critical alerts. Security advisories and threat notifications cannot share infrastructure with marketing campaigns. A marketing spam complaint that affects your alert deliverability puts your customers at risk. Use Postmark or a dedicated transactional service for critical communications.
The Enterprise Nurture Strategy
Cybersecurity enterprise deals typically require 6-18 months of nurturing. During this time, your prospect is evaluating multiple vendors, navigating internal procurement, and waiting for budget approval. Email keeps you relevant throughout.
The Monthly Cadence
Structure your enterprise nurture around a monthly cadence:
- Monthly: Threat intelligence digest with current landscape analysis
- Quarterly: Compliance framework updates relevant to their industry
- Event-triggered: Content downloads trigger deeper education sequences
- Milestone-based: Webinar attendance triggers demo invitations
Each touchpoint should provide standalone value that the recipient would miss if they unsubscribed. When every email teaches them something useful about security, they look forward to your communication rather than tuning it out.
Product Onboarding for Security Tools
Cybersecurity products with poor onboarding experience high churn because the customer never reaches the point where they see value. A structured email onboarding sequence prevents this by guiding customers through each deployment phase:
- Day 0: Deployment guide with step-by-step instructions and support channels
- After first scan: Celebrate first results and guide to next configuration steps
- Day 7: Advanced configuration for policies, alerts, and integrations
- Day 14: Best practices for ongoing monitoring and team collaboration
- Day 30: Check-in with optimization tips and success metrics
Track which onboarding emails are opened and which deployment steps are completed. Customers who stall at a particular step need proactive support, not just another email.
Building Trust Through Content
In cybersecurity, trust is the currency of business. Every email you send either builds or erodes trust. The companies that earn the most trust are those whose email content genuinely helps security teams do their jobs better - whether or not those teams ever buy the product.
Share original threat research, practical compliance checklists, incident response playbooks, and honest assessments of the security landscape. This content gets forwarded to colleagues, bookmarked for reference, and remembered when the buying decision comes. The cybersecurity vendor who has been the most helpful trusted advisor wins the deal.